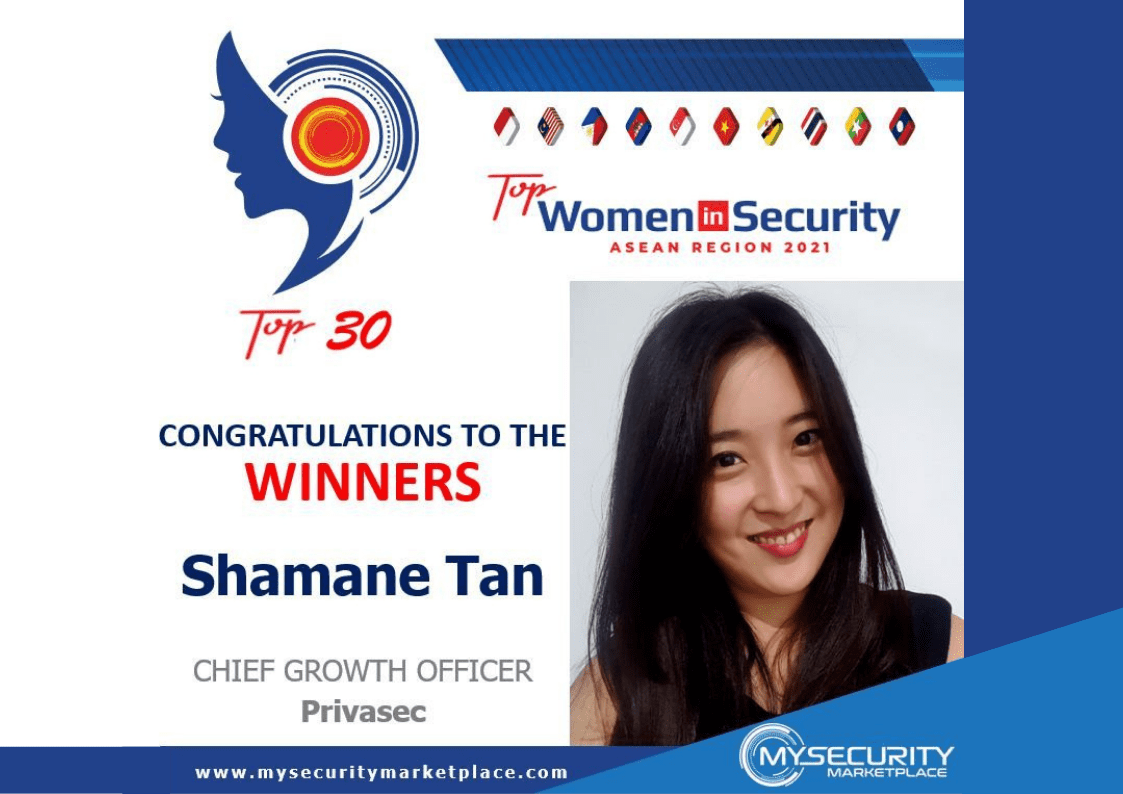
Shamane Tan Named Top 30 Women in Security ASEAN Region 2021
Red Team Attack Simulations mimic an adversary attacking your organisation. Red Team Attack Simulations enable you to understand and improve upon your ability to identify and respond to an adversary tyring to access your systems or information.
Shamane Tan Named Top 30 Women in Security ASEAN Region 2021 Read More »