Congratulations to our Senior Consultant’s big vulnerability find for VMware
Congratulations to our Senior Consultant David Roccasalva, for his discovery and responsible disclosure of a MFA Authentication Bypass vulnerability on VMWare Horizon DaaS (9.x, 8.x and 7.x) for VMware earlier this year.
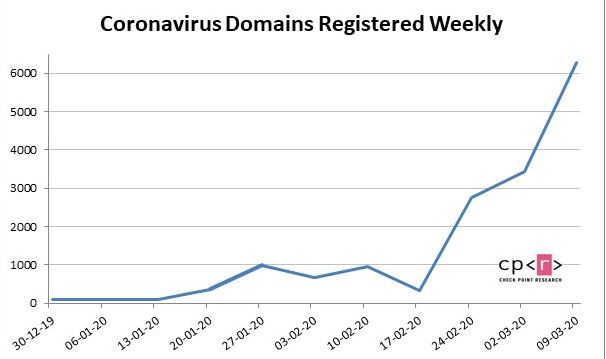
VMWare Horizon DaaS (Desktop as a Service) is a remote desktop and application service used by organisations for working remotely on applications, which is depended by many during the remote work situation as a result of COVID-19.
Congratulations to our Senior Consultant’s big vulnerability find for VMware Read More »